In 2020–2024, fraud targeting U.S. residents surged sharply, with call center-style scams becoming one of the largest sources of consumer losses. Viral claims (such as widely shared graphics asserting “Indian call center scammers stole $50.5 billion”) highlight public frustration, but the real answer requires careful parsing of data, structural vulnerabilities, and actionable reforms. Tackling these scams is not just about policing voice calls — it’s about reengineering the financial, telecom, and legal frameworks that make fraud so profitable. Only then can we credibly assert “this won’t happen again.”
The Federal Trade Commission (FTC) and FBI’s Internet Crime Complaint Center (IC3) report that Americans lost tens of billions annually to fraud, with phone-based and impersonation scams rising alongside digital payment methods. In 2024, the FTC stated that reported loss to fraud topped $12.5 billion, a historic high. The FBI IC3 reported over $16 billion in internet-crime losses in 2024, driven by schemes that often start as call scams and transition into remote access and fraudulent payments. These official figures show the scale far exceeds prior years and underscore systemic risks. (Source: FTC annual data; FBI IC3 annual reports.)
Understanding Operational Mechanics of Call Center Scams
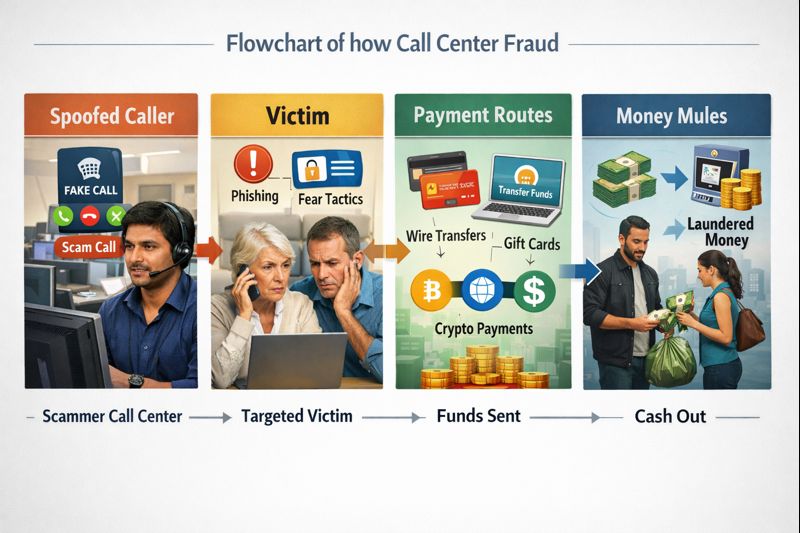
The business model for call center fraud typically includes:
-
Spoofed Caller ID & Telecom Abuse – Scammers use Voice-over-IP providers and spoofing to mimic legitimate numbers (banks, government agencies), bypassing basic caller-ID defenses.
-
Social Engineering Scripts – Agents trained to elicit trust, urgency, and secrecy, pressuring victims into payments or remote access.
-
Fast Money Movement – Once victim funds are obtained (wire, ACH, prepaid card, crypto), they are laundered through money mules and opaque payment chains.
These are not isolated phishing texts; they are distributed systems exploiting gaps in telecom governance and financial controls.
Why It Continues to Happen
Efforts to prosecute individual operators are important but insufficient. The core vulnerabilities include: